Secure SDLC Approach For Preventing Cyber-Attacks

According to CrowdStrike Report, a 50% increase has been analyzed in active intrusions and cyber-attacks in 2022. And the number may increase in 2023 too.
With more and more applications becoming a target of hackers, it getting complex for developers to identify relevant security approaches. Development teams are somewhere unable to select the best mechanism, which would be compatible, high-performing, and strong enough to prevent attacks.
But now the problem has been solved to some extent with the introduction of a Secure Software Development Lifecycle or Secure SDLC. It’s the fundamental approach, that every developer/security professional must understand. So, let’s get started to make software secure.
What Does SDLC Stand For?
Software Development Lifecycle (SDLC) is the step-by-step approach, used by software development teams to curate an application, website, or any other software piece. It helps them to define the procedures to follow for developing the application according to the client’s requirements.
Further, SDLC is of different types, such as Waterfall, Agile, DevOps, Spiral, Bigbang, and more. And all its models include the steps starting from gathering information and ending with releasing the software or constantly maintaining it.
The Traditional Software Development Process VS The Secure SDLC
In the traditional SDLC, there was plenty of room for vulnerabilities, as only the testing phase was available to make software secure. Due to it, cyber-attacks got to increase and companies started to face monetary, reputation, and data loss. To remediate it, industry veterans, came up with Secure Software Development Lifecycle.
With the introduction of Secure SDLC, vulnerable loopholes started to decrease, retaining data integrity, confidentiality, and availability. For better insight, look at the below differentiation table:
| Basis | Traditional SDLC | Secure SDLC |
| Primary Goal | To develop high-performance software with relevant security. | To build software with high security and performance, assuring CIA triad retention. |
| Phases Dedicated To Security | Only one Testing phase is available to find loopholes and patch them. | All phases focus on security from identifying security requirements to providing updates. |
| Main Focus | The main focus is on curating the application and aligning it with client requirements. | Creating an application with top-notch security mechanisms is the main priority. |
| Preference | Doesn’t get preference in comparison to Secure SDLC. | Always gets preferred for every software development. |
| Software Testing | Overall software gets tested. | Each software component gets tested as per the current phase. |
Why You Must Prefer Secure SDLC?
The answer to “Why you should consider Secure SDLC over Traditional SDLC?” consists of numerous reasons. And you find them all below:
Fewer Vulnerable Loopholes in Software
By following the Secure Software Development Lifecycle, you can identify vulnerabilities at an earlier stage. It will help you remove them before moving on to the next phase and releasing secure software for end-users. In addition, it will also reduce misconfigurations and the ability of attackers to exploit software.
Affordable Maintenance
One of the primary goals of software maintenance is to release updates to remove vulnerabilities and make them more stable. And to continue it, higher costs are required in traditional SDLC. However, with secure SDLC, the cost gets reduced, as the most vulnerable loopholes get patched during the designing, development, and testing phase itself.
Protection From Cyber-Attacks
Less the vulnerable loopholes, less the probability of getting attacked or breached. When you focus on security at each SDLC phase, you avail the insight of possible cyber-attacks on each component through multiple approaches. Further, such information gets used to configure relevant security mechanisms and prevent malicious actors in the future.
Recommended: What are OWASP Secure Coding Practices? Top 10 Web App Security Vulnerabilities
Compliance With Appropriate Standards
When you make security a priority, you automatically consider standards to follow and prevent legal actions. Standards such as HIPAA, HITECH, PCI-DSS, NIST, GDPR, and ISO are mandatory for applications of a particular type.
And if you don’t follow them, there’s a high probability of your software getting banned. But, secure SDLC makes sure to align applications with relevant protocols.
Unbeatable Collaboration For Security
In Secure Software Development Lifecycle, every team member from operations, developers, managers, testers, and business analysts, of them considers security. It helps the team to remove most vulnerabilities and develop a high-performing, project-goal-fulfilling, and end-to-end protected application.
Recommended: A Reference Handbook To Secure Software Development Framework
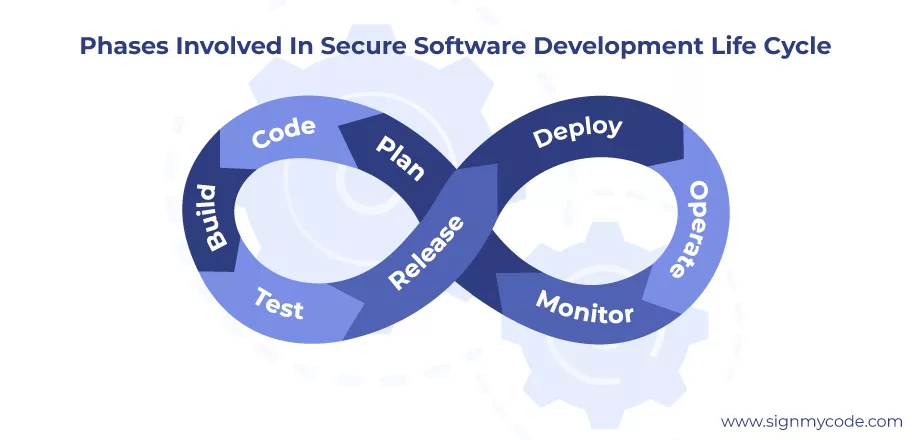
The Phases Involved In Secure Software Development Life Cycle
The phases in a secure SDLC are similar to the traditional SDLC. However, in all its phases, security is taken into consideration and processes get modified accordingly.
Phase 1: Planning and Information & Security Requirement Gathering
In the first phase, you need to gather, document, and verify all client requirements to identify associated stakeholders, project goals, timelines, and budgets.
At this stage, you will gain a clear idea of what type of application you will be building. Whether it’s going to be a web-based application, a mobile app, a cross-platform software, or something else.
And once you are clear about it, you need to focus on the following security aspects:
- Whether you will use encryption or hashing for protecting data.
- Which Code Signing Certificate will get used to make the code tamper-proof?
- What type of authentication mechanisms would get used to validate a user’s identity?
- Which SSL/TLS certificate will get installed for secure data transfer?
You need to think of overall software components and functioning to decide on appropriate controls to configure. Moreover, you must check CVE details for the technology, APIs, database, and other components to learn about possible vulnerabilities.
Phase 2: Architecture Designing and Prototype Generation
Once you are ready with all the requirements, it’s time to select the most accurate design for the application. Before you start designing the interfaces and internal connections using flow diagrams, consider the following security aspects:
- Select appropriate coding practices by consulting with security experts. It will help you prevent creating additional modules and reduce the attack surface.
- Create the design according to the selected standards, such as PCI-DSS, GDPR, NIST, and others, if any.
- Generate a hypothesis of attacks, which can get encountered and modify the designs accordingly.
In addition, you must create multiple designs, analyze them using threat modeling and verify, whether they comply with appropriate protocols. As a result, you will get the best from all designs, fulfilling project requirements.
Phase 3: Development as per Security Standards
Now comes the phase, where developers write the code according to and integrate multiple components into one. And also configure the security mechanism as decided in the previous phases. In the development phase, make sure that every team member is on the same page and updated with the project guidelines and goals.
Moreover, you must create a custom guideline for developers, such as:
- To not utilize code blocks from third-party websites.
- To not reuse the program from any other project.
- Perform unit testing before pushing the code into the repository.
- To dynamically review the code.
To make the process faster, you can also assign all such review and testing tasks to a particular team member.
Furthermore, you must also perform the following security practices:
- Utilize an EV Code Signing Certificate to tamper-proof the software and embed a digital signature.
- Configure input validation to prevent attackers from performing injection attacks through input fields.
- Set up multi-factor authentication and use hashing for password verification.
- Prevent the creation of backdoors, to lower the possibility of Remote Access Trojan attacks.
Phase 4: Software Testing and Vulnerability Patching
Besides considering software security at each phase, secure SDLC also provides a dedicated phase for testing. At this step, you need to perform penetration testing using both manual and automated tools. It would help you identify potential loopholes, leading to patching them before deployment.
For the most accurate results, take the help of Certified Ethical Hackers and Security Experts, who can test every software component. It will help you understand the attacker prevention strength of the application.
Further, you must focus on testing the following components:
- Input Validation
- Authentication, Authorization, and Access Control
- Error and Exception Handling
- Syntax
- Session Management
- Secure Data Storage
- Source Code Security
- Data in transmission
Additionally, you must consider using all major types of testing techniques, including Black-box, grey-box, white-box, and DAST testing.
Phase 5: Deployment in Secure Environment
After the development and testing, the task of deploying an application arrives. At this phase, you need to prepare the software for distribution.
However, make sure to always use a Trusted Code Signing Certificate before releasing. Otherwise, any malicious actor can modify the code, embed malware, and spread it by your name.
Moreover, to assure functionality, and security and to gather feedback, you can use the beta testing technique. Under it, only a few or selected stakeholders will get hands-on experience, which will help you patch vulnerabilities and update software components according to feedback.
Recommended: What is Code Signing SDLC?
Additionally, if you are using a cloud infrastructure, take help from cloud engineers to set up the environment. And once you complete all necessary tasks, release the software into the digital world through reputed online repositories and app stores.
Phase 6: Constant Monitoring and Maintenance
Now comes the last, but never-ending phase of a Secure Software Development Lifecycle.
In this phase, you need to constantly monitor the software behavior, its performance, and the working of security mechanisms. And you also have to store logs and analyze them frequently to make sure that everything is under control.
Additionally, you must consider the following checklist:
- Update software with the release of newer libraries and framework versions used in the software.
- Perform testing before and after the release of every update to patch vulnerabilities.
- Upgrade application to new vulnerabilities getting listed in the CVE database.
Additionally, you can participate in bug bounty programs to find additional risks and threats associated with the software. Create a maintenance plan and update it according to the new advancements in software development for stable and secure software in long term.
Wrapping Up
With the emerging security threats, Secure Software Development Lifecycle must get adopted by development teams. It would not be some drastic change, as the phases are similar to traditional SDLC but with a focus on software security. Moreover, it can get preferred for any type of development, using any SDLC model.
For fewer vulnerabilities and to accurately align applications with industry standards, preventing attackers and legal actions, secure SDLC is the need of the hour. And you must consider it for your upcoming projects.
Secure your Software Development Life Cycle with Trusted and Popular Code Signing Certificates by Reputed Certificate Authorities.
