Must To Know Secure Java Development Practices
Last Modified: September 18, 2024
Java is a top-notch software development technology used to curate desktop, mobile, and web-based applications.
According to enlyft, 455,000+ companies are using applications based on java.
But, with the introduction of newer technologies, hackers have become more competent in breaching, and Java apps are one of their primary targets. The main reason behind this is the occurrence of loopholes, including the Spring4Shell/Springshell vulnerability. In addition, more than 25 new Java vulnerabilities are added to the CVE database.
With such an increasing vulnerability rate, developers like you need to follow the best practices. It will help you utilize cutting-edge Java technology to build secure applications, and fulfill client requirements.
Want to Secure your JAVA Application?
Digitally Sign and Verify your Java-based Application or Code with Cheap Java Code Signing Certificate Just at $215.99/yr!
Best Practices to Build a Secure Java-based Software
You must consider the following best practices to curate a secure environment for a Java application to run its processes.
Avoid Implementing Serialization
Industry veterans, working as Java developers always suggest avoiding using serialization in applications. However, serialization helps in caching, sharing byte streams, configuring multi-tenant communication, and persistence.
But, there are also numerous vulnerabilities associated with it, such as an attacker can benefit from object deserialization to embed malicious code.
In addition, serialization also uses extensive processor resources, which can slow down the app’s performance and stability.
Furthermore, you must consider the following practices instead of serialization:
- Prefer JSON for data transfer
- Utilize non-native data formats, such as XML
- Deploy RASP (Runtime Application Self-Protection) tools on application servers
- Prevent classes from getting serialized by using the java.io.ObjectInputStream
Don’t Reveal the Exact Error
Revealing the exact error to end-users is a primary way of providing confidential information to an attacker. When you display the exact code, hackers use it to gather information about code structure, used libraries, databases, classes, and objects in Java software.
You must always keep your error messages generic rather than entirely technical. For instance, if a user enters the wrong password, only show a message such as “Invalid Login” rather than display the code behind password verification.
While developing the Java application, always create test cases to confirm that the error code is not displayed. Also, try to keep a log of every activity using tools like Kibana and Looker. Additionally, you can use a log server to analyze activities based on user behavior and detect malicious actors.
Encrypt and Hash Sensitive Information
Data has three states in Java applications: at rest, in processing, and in transmission. And you must focus on the security of all three. The best way to do so is by using encryption and hashing algorithms.
For data at rest, you must use encryption; hashing is the best technology for passwords. It will secure user passwords, even if an attacker successfully performs an SQL injection attack.
Further, you must use an SSL certificate to transfer every data bit in an encrypted environment. If you use a datagram for data transfer, then you can prefer configuring a DTLS (Data Transport Layer Security) for secure communication over the network.
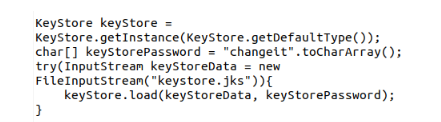
Below is a code example, which you can refer to to enable SSL.
Write Clean and Short Code
Clean and short code is the fundamental pillar of every secure Java software. Due to this, additional code gets removed, which directly impacts the elimination of additional vulnerabilities. The shorter the code and naming convention, the less the possibility of an attacker exploiting the application.
In addition, you must prevent reusing the code from third-party repositories, such as Stack Overflow and GitHub. Hackers are also present on these sites, and they publish their malicious code so that developers can copy it and put it in their programs. Hence, you must avoid code reusing.
Moreover, make perfect use of access modifiers by configuring different access levels to methods and classes. And try to provide only limited scope to components for interacting with each other and outside the network.
Prefer Only Tested and Known Libraries
To build a secure Java application, use only tested libraries to prevent attackers from exploiting your software. Before you use any library, research the CVE database to discover its vulnerabilities and associated patches. If the patch is unavailable, avoid using that particular library and find an alternative.
Whether it’s parsing, general-purpose, or logging library, always use it after confirming its legitimacy and available vulnerabilities. Also, constantly look at the release of their new versions to update your application accordingly.
Use Java Code Signing Certificate
To make the application secure in the production environment, it is always recommended that a Java Code Signing Certificate be used. Similar to data encryption and hashing, such digital certificates aid in encrypting the source code.
It converts the code into a hash digest and then encrypts that digest. The person with a private key only has the leverage to read or convert the code back to its original format.
Recommended: What is Java Code Signing Certificate?
As a result, attackers get disabled from reading and modifying the code.
Furthermore, it also embeds your digital signature, which helps the system identify you as an authorized publisher. Due to it, your users don’t face Unknown Publisher Warning, which boosts the user’s confidence and brand reputation.
Parameterize Input and Queries
According to Statista, SQL injection has led the charts of the most critical vulnerabilities in 2022. And the most common factor behind its successful execution is the lack of parameterization. To secure a java application, you must configure parameters in the code to run only specific queries.
public void selectExample(String parameter) throws SQLException {
Connection connection = DriverManager.getConnection(DB_URL, USER, PASS);
String query = "SELECT * FROM USERS WHERE lastname = " + parameter;
Statement statement = connection.createStatement();
ResultSet result = statement.executeQuery(query);
printResult(result);
}Using the code block above, you can create a difference between parameter data and a query. As a result, the attackers will get disabled from injecting malicious queries and breaching databases. Hence, your data at rest would become more secure.
Configure Authentication and Access Controls
Authentication is a crucial security control that every Java application must have. It will help you validate the user identity and allow only authorized people to access resources. You can prefer tools such as OpenID, Auth 2.0, and similar for strong and efficient authentication. However, you must verify their legitimacy before implementation.
Furthermore, configuring multi-factor authentication control should always be considered. It will help prevent hackers from hijacking user accounts through usernames and passwords.
To strengthen identity verification, you can also use cloud-based services, such as Firebase authentication. With it, managing and securing data will also be eliminated. But, you prefer it only if you have a flexible budget, as sometimes cloud services can be expensive.
Enable Java Security Manager
You won’t find Java Security Manager enabled by default, as it restricts a process from accessing the network, disk, processor, and other resources. But, according to security experts, using it’s a good practice.
Otherwise, someone exploiting a single Java app component could switch to another by jumping between processes. For instance, if you don’t enable it, a hacker can modify a running process’s bytecode.
Further, when you enable java security manager, you need to define policies for each process execution with its access level. As a result, each operation avails a limited exposure, which in return limits the attackers. Therefore, you must consider using the built-in security manager for a solid security foundation.
Concluding Up
Java is a top choice for companies that want to develop scalable business solutions. However, more vulnerabilities are discovered in Java every year, leading to exploits and breaches. Hence, developers must consider adapting the mentioned practices to prevent malicious actors from performing such activities on Java-based software.
Software Signing Certificates
Protect your Application and Software from from Malicious Attacks and Vulnerabilities with Reputed Code Signing Certs.
Cheapest Code Signing Certificates

