Private Key Generation and CSR Attestation with YubiKey Manager

Security is a primary concern in the modern digital world. Sensitive data is being transferred online at an increasing rate. Therefore it’s critical to keep it safe from unauthorized access.
This is where YubiKey steps in, adding an additional layer of security by creating and authenticating private keys.
The process of creating a set of public and private keys that may be used for various tasks, including data encryption and signing, is known as private key creation.
Data that has been encrypted with the appropriate public key is decrypted using private keys, which are kept secret. Private keys generated by YubiKey devices may be secured such that they never leave the device, making them impenetrable to hackers.
What is a Yubikey?

A YubiKey is hardware that offers safe authentication and encryption. In multi-factor authentication (MFA) systems, where a user must supply both something they know (like a password) and something they have (like a YubiKey) to confirm their identity, it is frequently employed as a second factor.
The ability to produce a pair of public and private keys is used for various tasks. This includes data encryption and signing, which is a feature of YubiKey devices. Because the private key never leaves the YubiKey, hackers and other malicious attackers cannot access it.
Recommended: What is a YubiKey? How Does it Work? [Detailed Guide]
Additionally, attestation, or the process of confirming the validity and integrity of a device or component, may be carried out using YubiKey devices. Through YubiKey attestation, a third party may confirm that the YubiKey being used for authentication is real and unaltered.
A utility for managing YubiKey devices is called YubiKey Manager. It may produce Certificate Signing Requests (CSRs) that act as requests to a certificate authority for a certificate.
To confirm that a CSR was produced by a legitimate YubiKey device, CSR attestation may also be done using YubiKey Manager. By doing this, it is made sure that the certificate being given is legitimate and has not been hacked.
About Yubikey Key Generation
Creating YubiKey keys is a straightforward operation that the users can accomplish with the YubiKey Manager program. Users may produce a pair of keys with the touch of a button.
Once produced, the keys may be used for several reasons, including safeguarding email communication and verifying user identities.
Recommended: What is Key Attestation for Code Signing Certificates?
What is Yubikey’s Attestation?
YubiKey devices offer attestation services in addition to private key creation. The process of certifying the integrity and validity of a device or component is known as attestation. YubiKey attestation guarantees that the authentication device is legitimate and has not been tampered with.
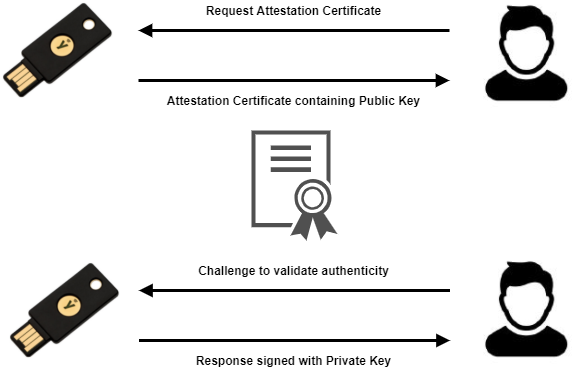
YubiKey attestation may be conducted by confirming the device’s cryptographic signatures. These signatures are created with a private key saved on the device and accessible only through a secure boot procedure. This prevents the signatures from being falsified or tampered with.
CSR Attestation with Yubikey Manager
Another method for using YubiKey devices to assure security is CSR attestation with YubiKey Manager. Requests for a certificate from a certificate authority are known as Certificate Signing Requests (CSRs).
To create CSRs and confirm that they were produced by a legitimate YubiKey device, use YubiKey Manager. By doing this, it is made sure that the certificate being given is legitimate and has not been hacked.
Video Guide to Generate CSR and Key Attestation using YubiKey Manager
Steps to Get Started with Private Key Generation
We will send you the key after verification and the order placement. Then you can authenticate your private key in this manner after the order is placed and verification is complete.
We have divided this entire process into THREE easy methods for a simpler understanding. Let us now begin!
Creating a Key Pair and an Attestation Certificate on your Yubikey
First, let’s look at how to generate a key pair and attestation certificate on your YubiKey. This can be done using the YubiKey Manager tool.
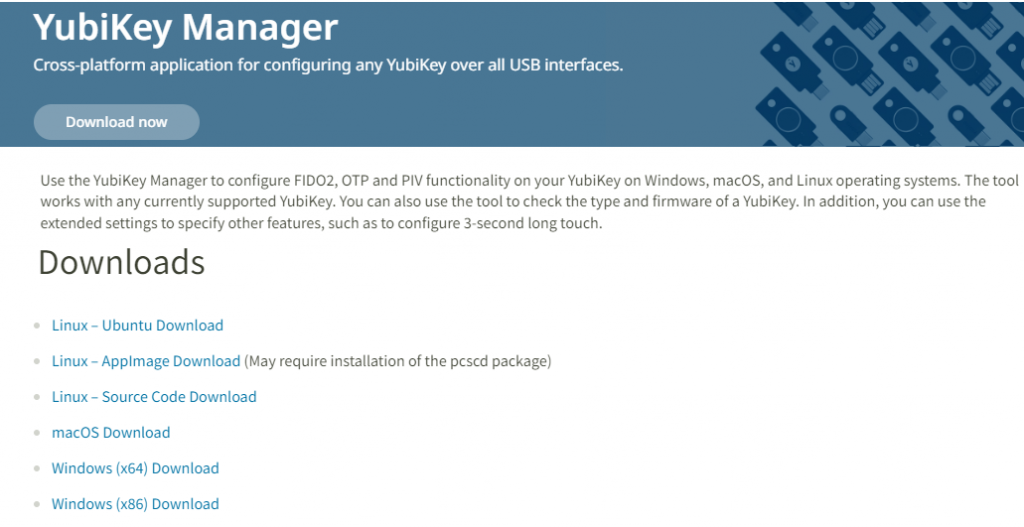
Step 1: To begin, you must Download and install YubiKey Manager from Yubico’s website if you still haven’t.
There are available versions for Windows, macOS, or Linux.
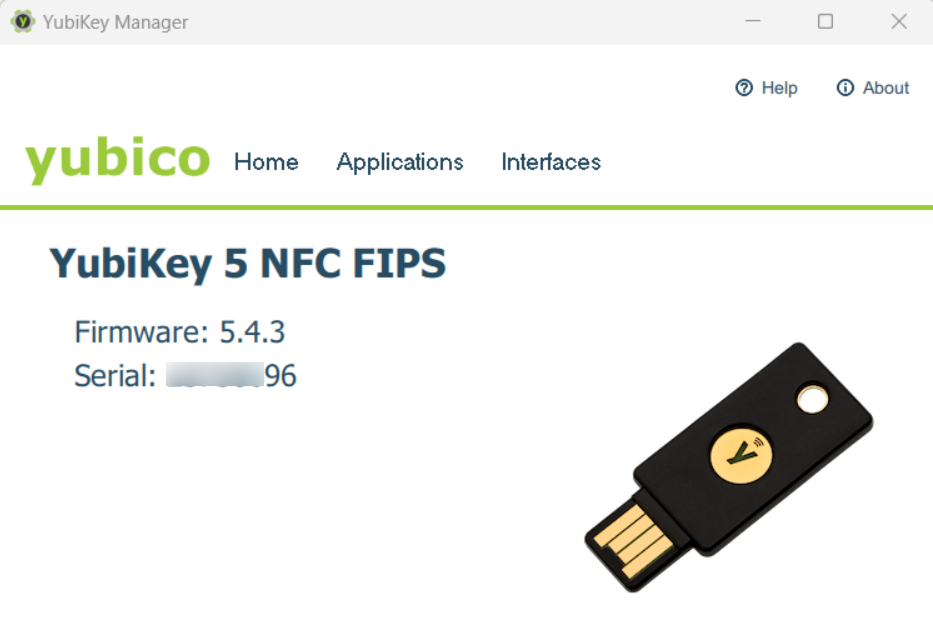
Step 2: Insert your YubiKey, then run YubiKey Manager. In the YubiKey Manager window, you can view your YubiKey.
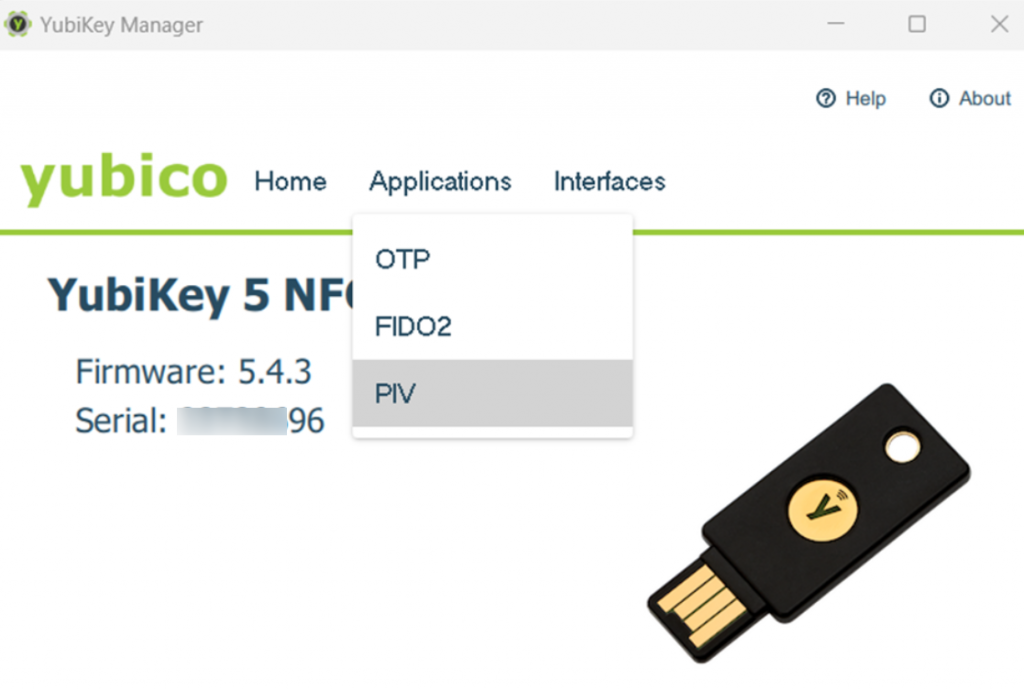
Step 3: Go to Applications and click PIV.
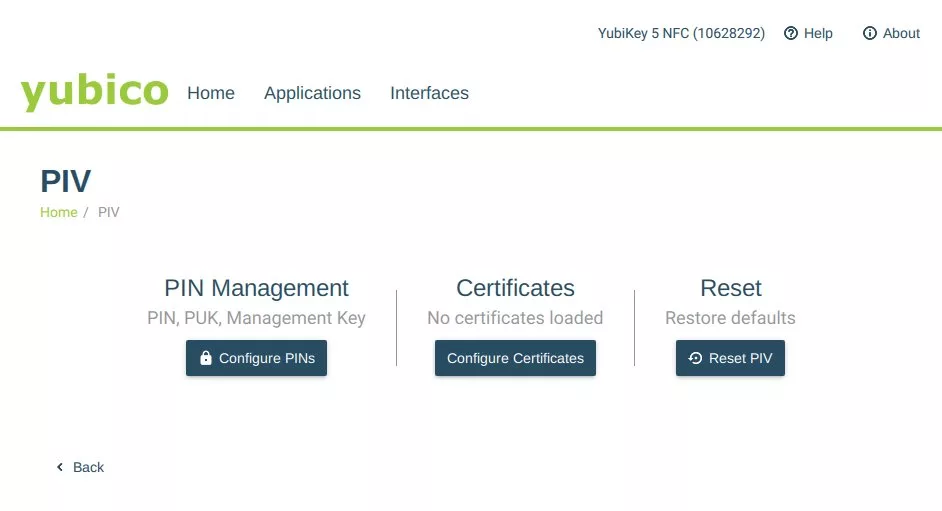
Step 4: Select the Certificates tab and then click the Configure Certificates button.
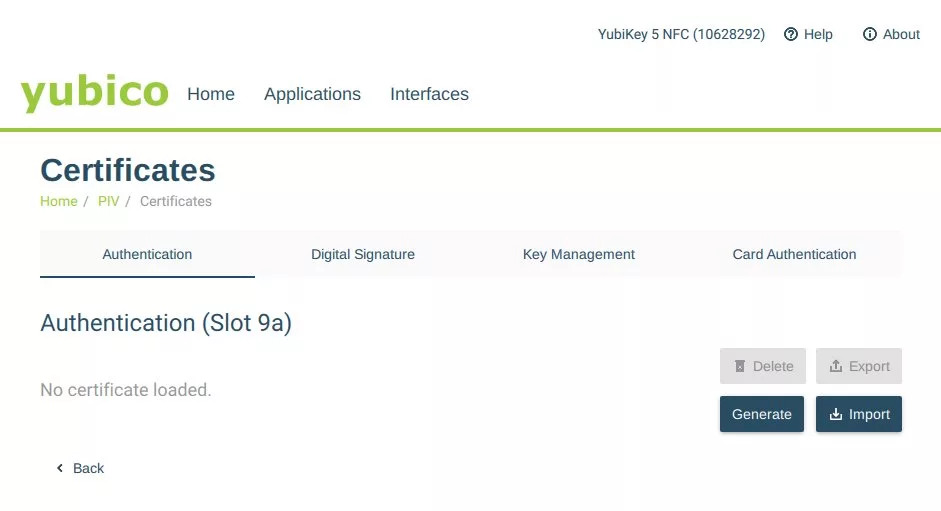
Step 5: Choose the YubiKey slot in which you want to go the key pair generation. Choose Authentication (slot 9a) when purchasing an token based OV and EV code signing certificate and Click on Generate.
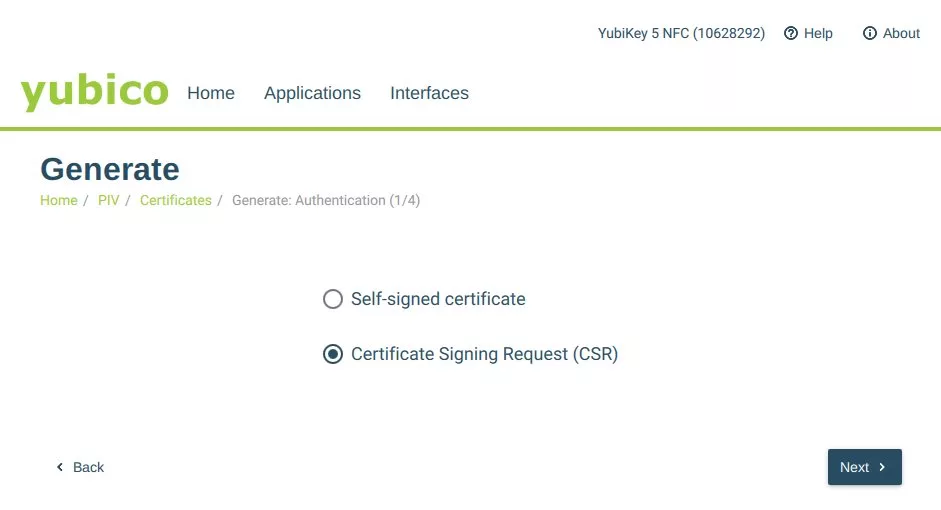
Step 6: Click the Next button after selecting Certificate Signing Request (CSR).
Step 7: To continue, choose an algorithm from the dropdown menu. For OV or EV Code Signing Certificate, choose either ECCP256 or ECCP384.
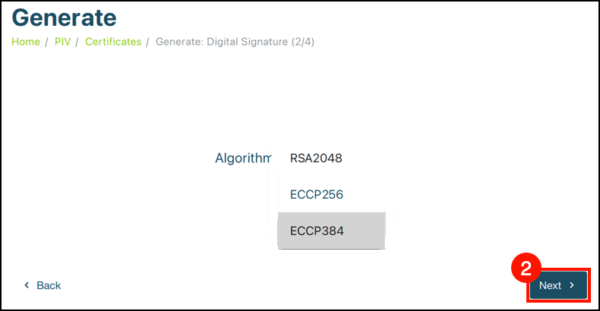
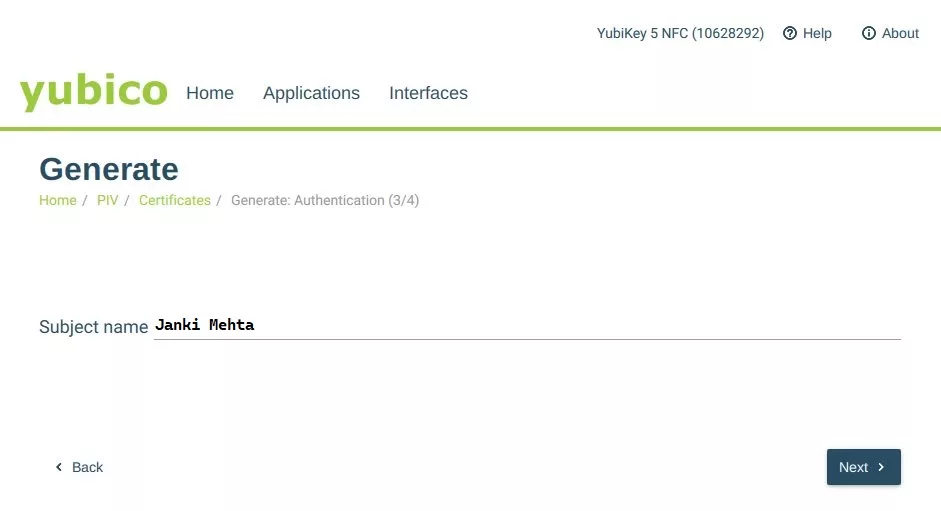
Step 8: After making your selection, enter a Subject Name for the certificate, and click the Next button. Keep in mind that we won’t be using this CSR for any actual purpose, it’s simply created as a byproduct of generating a new key pair.
Therefore, it’s not critical what you enter for the Subject Name.
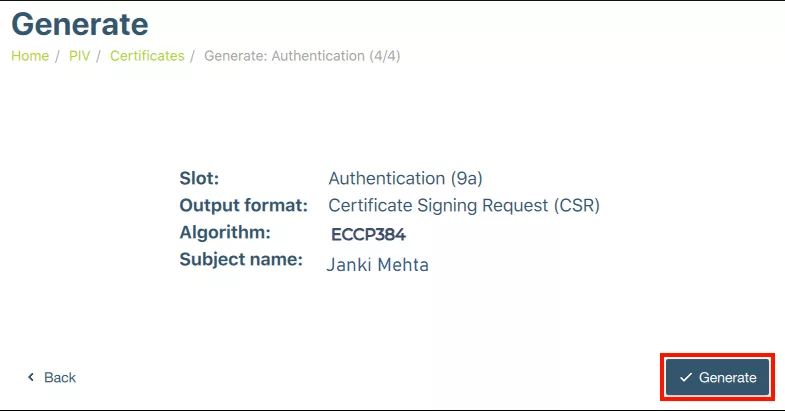
Step 9: Once this is done, click the Generate button.
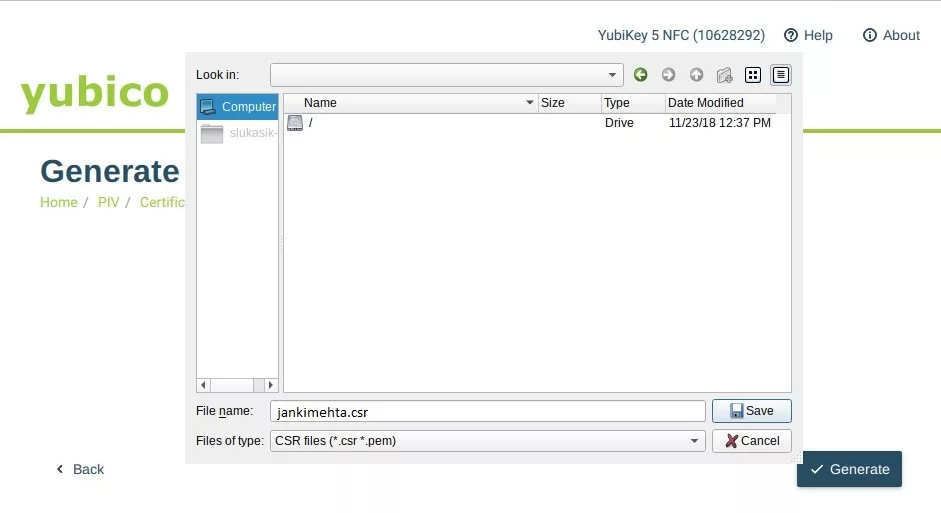
Step 10: You’ll then be prompted to choose a location to save the CSR file, create a filename, and click the Save button.
Step 11: Afterward, you must enter your YubiKey’s management key and click OK.
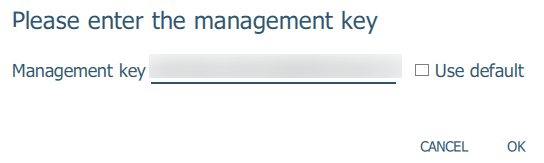
Your YubiKey’s Default management key is 010203040506070801020304050607080102030405060708
Step 12: Lastly, enter your YubiKey PIN and click OK. In case you require assistance finding your PIN, we are here to help.
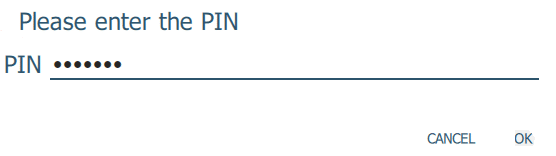
Your YubiKey’s Default PIN is 123456
Step 13: The CSR file will be saved in the location specified in step 10 of this guide.
Yubico provides a private key and a certificate preinstalled in every YubiKey, which enables the user to create an attestation certificate which will aid in verifying whether the private key is being generated on a YubiKey.
Generate Attestation Certificate
For this process, follow the below given command line.
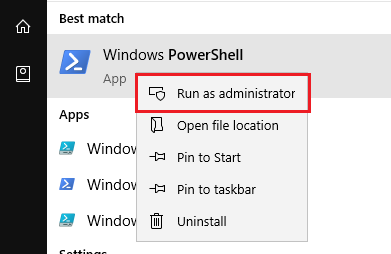
Step 1: To generate an attestation certificate, Windows users should open PowerShell as an administrator. While macOS and Linux users must try opening a terminal window on their devices.
Step 2: To access the YubiKey Manager files, use the following command:
Windows:
cd "C:\Program Files\Yubico\YubiKey Manager"macOS:
cd /Applications/YubiKey\ Manager.app/Contents/MacOSIf you are using Linux (Ubuntu), you don’t need to install the ykman command because it is already installed in your PATH.
Step 3: The following command should be used to generate the certificate (replace ATTESTATION-FILENAME.crt with the desired path and filename; if you used slot 9c, replace 9a with 9c).
macOS:
./ykman piv keys attest 9a ATTESTATION-FILENAME.crtWindows:
.\ykman.exe piv keys attest 9a ATTESTATION-FILENAME.crtLinux (Ubuntu):
ykman piv keys attest 9a ATTESTATION-FILENAME.crtStep 4: After that, access the slot f9 of the YubiKey for exporting the intermediate certificate using the ykman command (replace INTERMEDIATE-FILENAME.crt with the desired path and filename).
Linux (Ubuntu):
ykman piv certificates export f9 INTERMEDIATE-FILENAME.crtWindows:
.\ykman.exe piv certificates export f9 INTERMEDIATE-FILENAME.crtmacOS:
./ykman piv certificates export f9 INTERMEDIATE-FILENAME.crtNow that you have a verified attestation certificate, you can associate it with your EV or OV code signing order.
Wrapping up
In conclusion, YubiKey devices offer safe, private key generation and attestation services, which may be utilized to improve security in a range of applications.
YubiKey is a valuable tool in the battle against cybercrime since it can produce private keys that cannot be compromised and confirm the validity of devices and certificates.
EV Code Signing Cert
Digitally Sign your Windows 10+ Drivers, Kernel Mode Drivers, Packages with Highest Level Security and Assurance of EV Code Signing.
Price Starts at $279.99 Per Year