Must Know Approaches for Maintaining Mobile Application Security and CIA Traits
Last Modified: September 18, 2024
Nowadays, every business wants to reach out to a larger audience. And the best way for it is Mobile App Development. Whether someone is at work, at home, or somewhere outside, people frequently go through apps on their mobiles.
Such apps collect data, store it and process it to provide reliable results. Indeed, our sensitive and confidential data is also getting into the same process. Hence, it makes a top priority to focus on mobile application security. In this data-driven environment, maintaining data CIA must be at the top.
And, by reading further, you will understand every detail about it. So, let’s get started.
Overview of Mobile Application and their Types
The software an end-user runs on its mobile device is the application. Most example of a mobile app is WhatsApp, Instagram, PUBG, and even a calculator installed on mobile. Applications getting developed according to a specific goal and exclusive user requirements.
For instance, if you want to develop an app for an organization enabling its employees to share files and communicate. You will first analyze the types of communication mediums required by staff members and the formats of files getting shared. Further, you will develop accordingly and integrate all essential features.
Furthermore, there are three primary types of mobile applications:
Native Mobile Applications
Native applications run on a specific platform or operating system. Android and iOS apps are the most common example of it, as they run specifically on a single platform. You can’t install an Android app on an iPhone and vice versa.
Web-based Mobile Applications
Web apps require browsers to run. You have to access them through a mobile browser, but it will work smoothly as a native app running on your mobile device. Such applications help the user to save storage space on the device and access resources anytime through a browser.
Hybrid Mobile Applications
As the name define, Hybrid apps are a combination of Native and Web-based applications. You have to install them on your device, but some of their functions automatically redirect to the browser for execution. In addition, one more hybrid app exists that can execute operations on both Android and iOS-based devices.
Unleashing the Reason to Focus on Mobile Application Security
Nowadays, whether people are at work, college, or home, most of them are on their mobile utilizing some application. And every mobile app requires some input, which it processes to provide the required output.
The data collected by an app can be personal, financial, or any other confidential information.
Therefore, focusing on secure mobile application development is necessary to maintain the confidentiality, integrity, and availability of such data.
Moreover, it’s also crucial for the following reasons:
- To secure mobile devices from malware attacks.
- To transmit the data between users in a secure communication channel.
- To process each data bit in a protected digital environment.
- To ensure data integrity for all the end-users.
- To build a reputation for the company, it develops and offers secure applications.
- To align with industry standards and prevent legal actions.
Process and Mobile App Development Checklist
For crafting a mobile application, developers undergo a set of steps as follows:
Step 1: The team gathers Requirements, and analysis gets performed to define the scope.
Step 2: The project team generates a budget and timeline according to needs.
Step 3: Designing gets started, following the testing of prototypes.
Step 4: Mobile app development starts, and unit testing gets performed.
Step 5: The testing team verifies functioning, finds loopholes, and work with developers to provide necessary updates.
Step 6: App gets available to the end user, and the development team performs frequent maintenance operations.
All the steps mentioned are mandatory to follow for building any mobile application. However, there is an additional checklist, which you can also consider for security purposes.
It includes the tasks:
- Secure the code using Code Signing Certificate.
- Confirm that all data communications are encrypted.
- Verify the working of the Authentication, Access Control, and Authorization system.
- Perform Compatibility test.
- Run the application on different versions of the platform and update accordingly.
- Test all the third-party APIs.
- Validate the app’s connectivity with the server and vice versa.
- Validate whether all the user needs are getting fulfilled or not.
Most Common Mobile App Vulnerabilities, Causing Heavy Losses
Following the appropriate development, the approach gets always considered the best mechanism to curate a secure application. However, some factors still lead to open vulnerable loopholes in the mobile application.
Using Outdated Frameworks
Using outdated mobile app development frameworks is what an attacker requires. Outdated technologies have vulnerable components exploited by hackers in the past.
Also, mechanisms to exploit such vulnerabilities can get easily discovered over the internet. Thus, it makes it easier for malicious actors to understand the application, its functioning, and its internal structure.
Therefore, spreading malware, performing code injection, and modifying software code becomes seamless.
Minimal Protection across Data
Protecting only APIs and other components is not enough, as data is also a primary element. Hackers can breach and read if you store and process user input and any additional information in its original format. It will expose the customer details, and the organization will face heavy penalties.
In addition, configuring a traditional database system can cause data reputation and inconsistency. Besides the data at rest, if your app transfers data in its raw format, any attacker spying on the network can interfere with it. The content can change, the virus can get embedded, or credentials can be stolen.
High Usage of Third-Party Components
While developing any mobile application, it’s obvious to use some third-party APIs. However, utilizing them in more quantity can be a primary disadvantage of your applications. Besides degrading platform compatibility, performance, and quality, it is a severe cyber risk.
If any third-party component is not from an authorized publisher, it can contain some malicious script or code. Moreover, attackers can get a more significant number of chances to find vulnerabilities. They will have additional elements to go through and find a loophole in the application.
Access to a third-party component can sometimes lead your user network to face data breaches. A minimal app component can become the reason for a high reputation and revenue loss.
Not Using Accurate Programming Methodology
Programming methodology is the foundation of mobile applications. If you start writing code without defining the structure, many bugs and errors can arise. Your users will face unattended exceptions, lowering the performance and quality.
It can also weaken the overall app architecture, leaving the room open for hackers. It can lead them to gain unauthorized access, perform data theft, spoofing, and spread malware.
Lack of Authentication and Authorization
Configuring appropriate authentication and authorization must be a priority while developing any mobile app. It allows only legitimate users to communicate with the server and utilize resources. However, if your mobile app lacks both these security measures, it is vulnerable to spoofing and brute force attacks.
Furthermore, it can lead attackers to reside in the network for extended periods and execute an enormous cyber-attack.
Approaches to Make Secure Mobile Application
You must follow the following best practices to make the mobile application secure and promising data CIA traits. It will aid you in preventing potential cyber-attacks and patching vulnerable loopholes.
Complete Data Encryption
Encryption is a basic necessity of every mobile application security. You should always configure it for data at rest and in the communication channel. It uses advanced mathematical calculations to convert files into an unreadable format.
You must use an SSL/TLS certificate for securely transferring data between the app and server. Additionally, you should set up a hashing mechanism that must hash all the user input and store it in that particular format.
Usage of the Latest Framework
Whether you are building a native, web-based, or hybrid app, prefer only the latest frameworks. It will help you achieve the highest level of security, as its developer must have provided compatibility, data protection, and performance updates.
Besides this, it will help reduce vulnerabilities in your mobile application. And the probability of getting attacked will get reduced, as hackers will not find any loophole available in previous versions.
Frequent Updates
As the new updates of frameworks, programming languages, and APIs get released. The app developer must provide the same upgrades to end users. It will aid you in achieving the two goals:
- The app will follow the latest standards, ensuring the utmost performance metrics.
- Your app will get additional security upgrades, preventing cyber risks and threats.
Multi-Factor Authentication
You should only allow legitimate users to access the application, and to ensure it, multi-factor authentication is the best mechanism. It will verify the user details through two or more modes and then only allows to utilize the mobile app.
As a result, you can prevent spoofing and brute-force attacks. For instance, when a stakeholder inputs its username and password, the system will send an OTP to its number or email. When the OTP gets entered then, only access will get granted. Therefore, the attacker will get stuck, even after gaining the credential details.
Appropriate User Privilege Management
Every app has different kinds of users. It can be an administrator handling the backend or an average end-user performing operations through the interface. Hence, it is essential to provide accurate access to each kind.
For instance, if you provide administrator control access to an average end-user and its account gets hacked. Then, it can lead an attacker to gain access to the complete application architecture and perform unauthorized modifications. Therefore, you should define the features required by a particular stakeholder and configure them accordingly.
Proper Session Handling
Most people don’t log out using mobile applications, as they close the app directly. It makes crucial for developers to curate a function disabling the session once the user leaves. It will help to prevent attackers from breaching the session token. Moreover, for financial transaction-based applications, a session expiration timer must exist.
Utilizing EV Code Signing Certificate
Code Signing Certificate is the best mechanism, which you must opt for for your mobile applications. Besides making the complete code tamper-proof, it enhances the brand reputation across platforms.
An extended validation code signing certificate would be perfect. You will get an instant boost to your business reputation.
In addition, you will get the private key in an external USB, working as an additional security layer. You can store the key anywhere and disable crackers and hackers from making unauthorized changes.
Securing the Most Used Apps: Approach to Secure Android Application
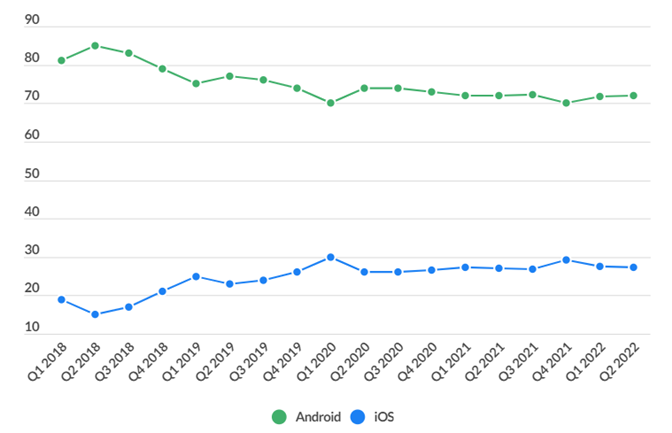
Android Applications have the most significant number of users around the globe. According to Business of Apps, more than 70% of smartphone owners use Android applications. Therefore, it makes every mobile app developer understand the best practices to secure android applications.
Below are the top approaches you should keep on priority while developing an Android application.
- Configure signature-based permissions for better and more secure file access.
- Ask the end-user to input account credentials before displaying sensitive information.
- Build and integrate a custom trust manager to accept only reliable digital certificates.
- You should enforce read and write permission according to account type.
- Prefer the device’s storage to store confidential information.
- Enforce the app to not process files with the unstable format.
- Frequently update dependencies, such as development libraries and security upgrades.
- Set up the app to hold only non-sensitive information in the cache storage.
- Always utilize a Code Signing and SSL Certificate.
Wrapping Up
Mobile application security is as crucial as desktop app security. Users make financial transactions, store sensitive information, and share confidential files over such apps. And, if your app has any potentially vulnerable loophole, it can result in identity theft, data breach, and heavy monetary losses.
Therefore, developing an application that aligns with the correct approach and follows the checklist are essential. Moreover, you should always configure the latest authentication and authorization mechanism, handling user privileges effectively.
Trusted Code Signing Certificates
Prevent Code Tampering and Authenticate Code Integrity by Digitally Sign your Code with Trusted Code Signing Certificates.
Get Code Signing Certificate

