How to Hash a File to Improve Software Security?
Cybersecurity is integral for the successful functioning of any online organization. This type of digital security ensures that your organization is safe online.
It helps keep a variety of malicious activities at bay from your online company that can potentially tamper with the confidential data of the customers. While Code Signing Certificate can help beat this risk, it is not all. Hashing is also used as a potential method to provide paramount security against these problems.
Hashing involves the process of transforming a string of characters into another significant value. The aim is to render a great amount of security using a one-way encryption method. So, unlike the code certificates where encryption keys are used, the Hashing process uses a more valuable method of ensuring security.
It is believed by experts that Hashing provides robust security that allows the impossibility of data decoding. The hashed values are very complex and hard to crack by any third-party penetrators. For this purpose, we will help you understand Hashing more vividly today.
Applications Of Hashing
- Hash is implemented in many well-known programming languages like Java and Python.
- It may be helpful in indexing.
- It may help execute caching systems.
- The hash may also be useful for the process of load balancing algorithm.
- You may also experience hashing in diverse cryptographic algorithms.
- Its utilization also occurs in disk-related data structures.
What Are The Pros And Cons Of Hashing?
Other data structures may not be as great in terms of synchronization as hash is. In fact, the hash may also be more space-efficient, easy to use, and consistent than other security-related technologies.
Experts also believe that hash tables are more effective than search trees. In fact, hash tables are also better in terms of data retrieval and provide better speed along with good manipulation.
Although Hashing comes with a sea of advantages, it may also have certain disadvantages attached to it. For starters, the hash may not be very effective during too many collisions. It may also not authorize any null value.
Apart from this, hash tables may not be very easy to execute, and they have a restricted capacity altogether. That is why the tables may ultimately be full sooner.
How To Prepare For A File Hash?
How To Choose The Best Type Of Hash?
A potential hashing function that caters to all your needs is critical. So, when you are selecting a hash, make sure it adheres to all your needs. For starters, your preferred hash must be able to distribute the keys in a uniform order. This means every table position must be equally built for every key.
Recommended: What is Hashing? Best Hashing Algorithms
Another thing to scout for is that your preferred hash must be effectively commutable. Also, remember that any good hash function generally contains the last three digits. You must also want to know that many potential hashes are created using heuristic techniques.
How To Create The Hash?
Did you know that now you can indulge in file hashing within a minute? This guide will help you know how!
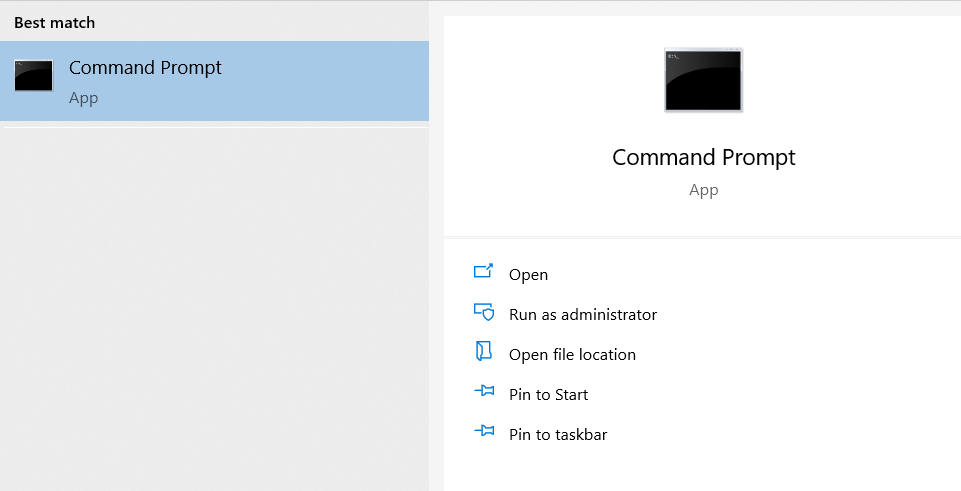
- Tap on Windows Command Line. In your Start section, write CMD and tap on Enter. This will redirect you to the Windows Command Line.
- After this, you need to select the hashing algorithm you wish to leverage.
- Remember that every hash function is created to cater to different requirements. So, you need to choose one that is suitable to your preferences.
- Now Hash a file with the help of the CertUtil -hashfile <file path> SHA256
For E.G:certutil -hashfile c:\demo\demotest_file.txt SHA25
That’s all. How simple is that you hashing file is on way! Once done it looks like 8wc41cbbfc21619e1d51dd729dbd9dd73abaujn98625222
How To Verify that the File Has Been Hashed Correctly?
Whenever you are using open source software, you must always check their Comodo Code signing Certificate or any other digital signature. But if it does not have one, it becomes more important than ever to check if it has a cryptographic hash.
If you are confident that the site you are using does not have a fake cryptographic hash, then examining the value of its hash is better than doing nothing.
For this purpose, create a note of the hash number that is published. This will be done by the developer themselves.
Get the value of the hash file that you have with you for software security.
Now, run a comparison between the two hash values. If both the hash values match one another, then all is well.
How To Use The Right Verification Tools For Hashing?
If you want to make sure that the hash was generated properly, the use of the correct tools is important. The right tools will help provide the right amount of security along with minimal risks of inaccuracy. For starters, the use of an antivirus file to make sure that the hash is free from any form of malicious activity is necessary.
Apart from this, you may also require a hash tool that helps to run an estimate of the hash of diverse files. You can also use hash checkers online to verify your hash and ensure its full security.
In case you want comprehensive solutions regarding this, SignMyCode can be very effective. Remember to only choose hash tools that are authenticated and legitimate for online purposes. You can also seek the assistance of a technical expert to help you understand which tools can be the best pick for you.
Winding Up!
Hashing is a simple yet complex process if it is not understood properly. In this guide, we have laid out a step-by-step process for you that will enable you to conduct hashing securely. Also note that although hashing and encryption are often used interchangeably, they are both quite different from one another.
While encryption runs on encryption keys, hashing turns out to be a more secure method. It does not use the power of these keys to function. Also, the hash is supposed to support three main operations. They are insert, delete, and get (key). This is how hash can be useful for you.