Self-Signed vs. Publicly Trusted CA Code Signing Certificates: What to Choose?
Last Modified: September 18, 2024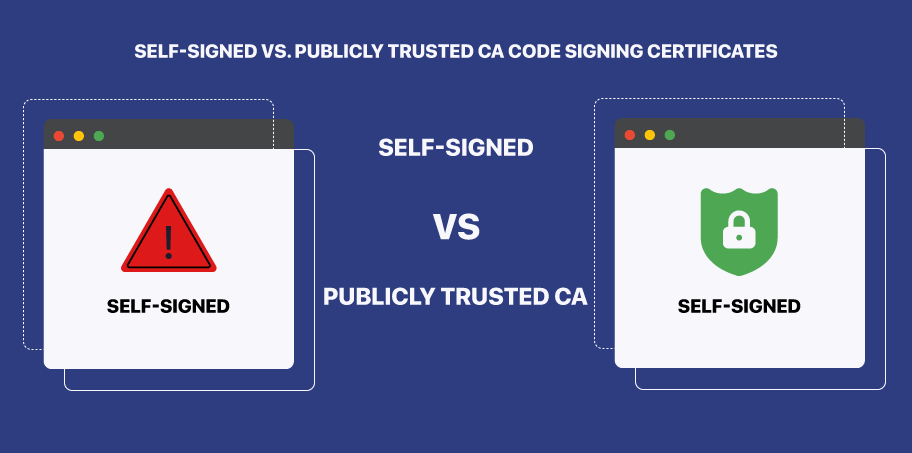
Being a developer, it has become your moral responsibility to offer clean and safe software products for users to install on their systems. You can easily tackle this by signing your software code and other executables with a digital security certificate.
However, doing so requires purchasing a code signing certificate from a renowned and respected Certificate Authority like Certera, Sectigo or Comodo, or DigiCert. Buying a certificate from them can be expensive, that’s why most developers and programmers think of publishing their executables with a self-signed certificate.
It can seem an attractive choice due to the associated cost savings. But before you jump into anything or publish the software with a self-signed certificate, consider reading this article till the end. Let’s understand the self-signed certificate vs CA certificate and what to choose:
What is Self-Signed Certificate?
A self-generated certificate is a certificate created and entrusted by the publisher of the software. It’s not issued or signed by any CA or distributor and can’t be used for online publication. The only purpose a self-signed certificate serves is to use the signed executables for internal usage.
Since you only trust and vouch for the signature of a self-signed certificate, it’s best to use the same for testing and development purposes. The operating systems or browsers won’t recognize this signature and label it as not secure and show the unknown publisher warnings.
Another issue with self-signed and generated certificates is they can’t be timestamped. Thus, the only use case of the self-signed code signing certificate is to use it while software and applications are in a testing environment.
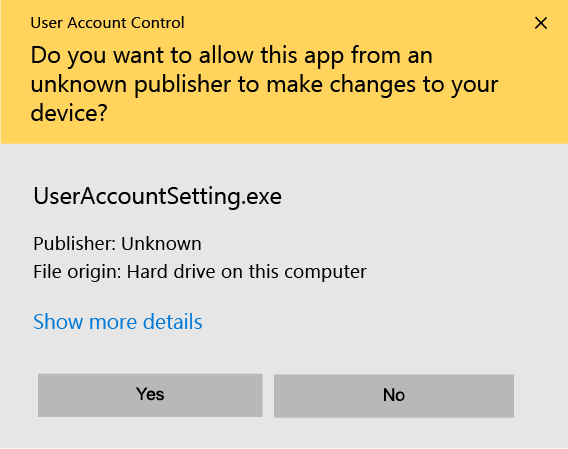
And if the software apps are published with the self-signed certificate, the OS will display the following alert:
What is a Publicly Trusted CA Certificate?
A publicly trusted code signing certificate is issued by renowned certificate authorities (CA) or their certificate distributors. CAs issue a certificate only after rigorous validation and verification process. They require each publisher to undergo a certain level of verification to prove their legitimacy and authenticity.
Thanks to that standard or extensive validation, the certificates issued to them act as a mark of trust for software users. It signifies that the software is coming from a genuine source and hasn’t been modified or altered since the certificate is issued.
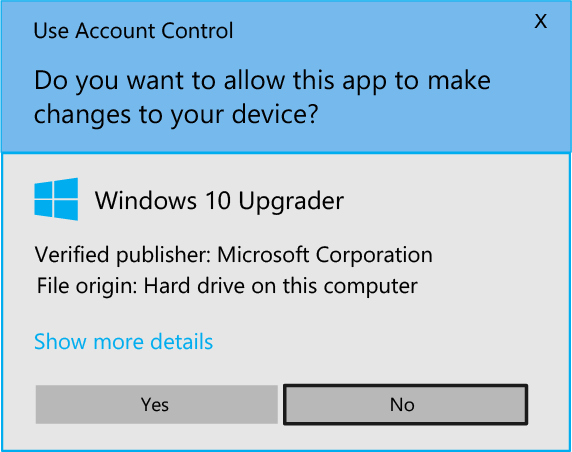
Moreover, the users can download, install, and use software signed by a CA without getting any warning messages or alerts. The Windows installation wizard will show that the software is from a verified publisher as seen in the image below:
What is the Difference between Self-Signed vs. Publicly Trusted CA Code Signing Certificates?
- Standards & Policies
- Warning Message
- Authenticity and Integrity
- Types of Validation
- Certificate Revocation
- Time Stamping
- Expiration Period
- Cryptographic Functions
1. Standards & Policies
In a self-signed certificate, developers and publishers set their own policy, which is not recognized or trusted by others.
Certificates issued by trusted CAs follow standards set by industry forums like CA/B that are trusted by browsers and operating systems.
2. Warning Message
While installing the software with a self-generated certificate, the operating system will throw an unknown publisher warning.
Software and apps signed with trusted CA certificates won’t display any warning and show that the software is from a verified publisher.
3. Authenticity and Integrity
Users or recipients of the software with self-signing certificates can’t verify the authenticity or integrity of the publisher.
Users of the executables signed by publicly trusted CAs can verify the authenticity and integrity of the publisher.
4. Types of Validation
In a self-signed certificate, there are no different levels or types of validation for certificate issuance.
Certificates issued by CAs have two different levels of validation: Standard Code Signing Certificate and EV Code Signing Certificate.
5. Certificate Revocation
A self-signed certificate can easily be compromised by hackers and can’t be revoked, making the executables vulnerable.
If the code signing certificates issued by trusted CA or distributors are compromised, the publisher can easily revoke them within hours.
6. Time Stamping
There is no way for publishers to time stamp their self-generated certificates.
While the same for CA certificates is possible, which will keep your executable and software valid even after the expiration date.
7. Expiration Period
Typically, a self-signed certificate has a longer period of validity, which is counterproductive as it will be exposed to the latest software vulnerability.
The Best Code Signing Certificates from CA have an expiration date of up to 1 to 3 years. So, you’d have to renew it to equip yourself with the latest encryption standards.
8. Cryptographic Functions
A self-generated certificate might use lower cipher and hash technologies which makes it less secure.
Certificates from CA, on the other hand, incorporate the latest hashing algorithm and cipher technology.
Conclusion
So, here you go! For better understanding, we have extensively covered different aspects of self-signed certificates vs CA certificates.
Now that you are equipped with such knowledge, we hope that you’ll be able to make better and informed decisions. As you know, self-signed certificates are best suited only for software in the developing and testing phases.
So, when you decide to publish your software online, you must Purchase a Cheap Code Signing Certificate from a trusted CA or their distributor.
Buy Code Signing Certificate
Increase your Software Downloads and Verify its Integrity by Digitally Sign Software and Executables using Trusted Code Signing Certs.
Price Starts at $215.99 Per Year

