Cyber Security Statistics of 2023: Eye Opening Facts

In today’s one-click world, organizations of all sizes should be committed to improving their cyber security posture. Helping them to mitigate the risk of a data breach and protect their critical assets. This means having the right technology, processes, and people to monitor the environment and respond to incidents quickly and effectively.
According to a recent IBM analysis, the average cybercrime takes 280 days to detect and contain and costs businesses up to $3.86 million. As cybercrime becomes more common, it’s critical to grasp the whole security situation and be prepared to defend yourself and your business.

A data breach may cost hundreds to millions of dollars, and the harm to a company’s reputation can be disastrous. The worldwide epidemic has further worsened the cyber security situation, with firms experiencing a 600% surge in cyber threats.
Businesses should stay updated with the latest cyber security statistics to understand the risks better and keep their security posture current.
In addition, organizations should have a comprehensive security program to safeguard their data. The latest tools and technologies are a must to detect and respond to threats in a timely manner.
Recommended: Best Safe Download Checker Tools to Protect Your Devices from Threats
For companies looking to protect their data and make the most of their cyber security investments, understanding the latest cyber security statistics of 2023 can make a world of difference.
With the right security posture and people in place, companies can protect their assets and take steps to prevent data breaches.
How did the Covid-19 Pandemic Impact Cybersecurity?
Can you reminisce Zoom meeting? Of course, you can! Who might not have had a Zoom call during the lockdown? But what if we tell you that Zoom was hacked in 2020, leading to settling about 500 thousand accounts? Well, that’s true because the hackers sold these users’ account details on the dark Web.
Companies found it increasingly difficult to handle their security demands tightly when the globe transitioned to remote work due to the COVID-19 epidemic.
Unfortunately, this lack of protection has returned to haunt them, with the typical data breach costing $137,000 more than previously.



In addition to the financial costs, 20% of managers have reported security breaches caused by remote workers.
18% have acknowledged that cybersecurity isn’t one of their top five concerns.
To make matters worse, 44% of employers did not give cybersecurity training to workers working from home.
It is obvious that the absence of security during the epidemic had a significant impact on businesses, but how did this happen? Due to a lack of infrastructure and training, the unexpected move to working from home has left security underperforming.
Because most firms were unprepared, they had to scurry to meet remote work needs and close security breaches.
Fortunately, there are methods for monitoring the consequences of a data breach and protecting your company from additional harm.
Strict security standards, frequent training, and remaining current with the newest protocols are all necessary to protect your firm’s security. Businesses may safeguard their assets and personnel from possible threats by remaining watchful.
Increase in Covid-19 Rising the Cybercrime
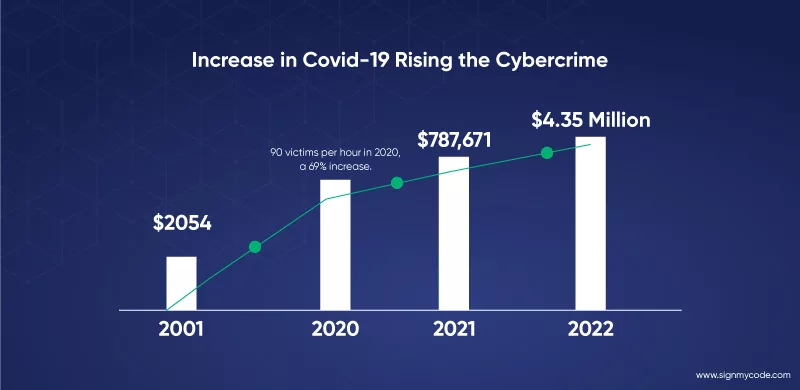
The year of the Covid-19 epidemic has caused a change in the occurrence of cybercrime from 2019 to 2020.
In 2019, 53 victims were recorded per hour, according to the data, but the pandemic caused this number to rise to 90 victims per hour in 2020, a 69% increase.
The average cost of data breaches per hour has also gone up internationally. A person’s average hourly cost in 2001 was $2054; by 2021, that cost had increased to $787,671; by 2022, it had reached $4.35 million.
As a result of the epidemic, the digital revolution has quickened, and more businesses are choosing to go online. As a result, more information and resources are exposed to cyberattacks, and criminals are utilizing this opportunity.
Businesses are developing better security solutions. The escalating rate of cybercrime has outpaced these safeguards, which have fallen short.
There is an increased risk in various industries, including banking, healthcare, and public services. Resulting in a sharp rise in cybercrime, with several businesses being victims of fraud and data breaches.
Although cybersecurity experts worked long hours to spot and counter emerging threats, the epidemic negatively impacted the entire sector.
Organizations should proactively develop improved security and risk management procedures to combat the rise in cybercrime. This comprises investing in more advanced technology and equipment to recognize, stop, and respond to cyberattacks.
They should also provide policies and practices to safeguard their systems and data.
With such a dramatic shift in cybercrime, organizations must be vigilant to protect their data and systems.
Current Statistics for Data Breaches and Malicious Activities on Web
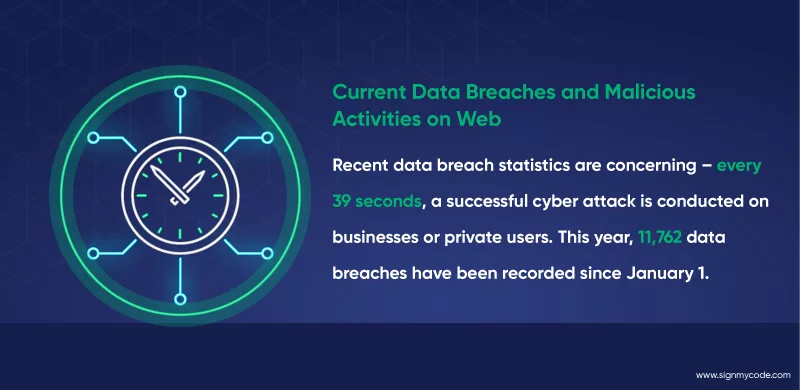
Recent data breach statistics are concerning – every 39 seconds, a successful cyber attack is conducted on businesses or private users. This year, 11,762 data breaches have been recorded since January 1.
Fortunately, the cybersecurity industry is vigilant in detecting and blocking such attacks, preventing 99.9% of all cyber threats. To stay safe from the remaining 0.1%, businesses are encouraged to invest in security standards, good data management processes, and employee awareness training.
The Department of Homeland Security recommends that organizations should spend at least $2,691 per employee annually for their cybersecurity needs.
Data breaches are a serious concern, and according to current data breach statistics, hackers always make cyber attacks. In fact, there is an average of 2244 cyber attacks per day worldwide.

Fortunately, the cybersecurity industry is very good at preventing data breaches. Many companies are investing in cyber security measures to protect their data. With the right measures in place, most cyberattacks won’t be successful.
According to reports, companies should spend just $2,691 per employee annually to minimize data breach risks.
When a company experiences a data breach, the cost can be enormous. Many of these breaches greatly affect companies and their customers.
It’s clear that hackers always make cyber attacks, but fortunately, the cybersecurity industry is progressing in preventing data breaches. Make sure you buy code signing certificate in time.
With the right investments and preventive measures, companies can minimize their risk of suffering a data breach.
A Scenario of Cyber Crime in 2022: An Elevation in 2023

According to the latest research from Check Point Research, the number of global cyberattacks is expected to increase by 38% in 2022 compared to 2021.
This increase can be attributed to an increase in the number of sophisticated hackers and ransomware groups, as well as a greater reliance on collaboration tools by remote workers, e-learning platforms by schools and universities, and a dramatic rise in attacks on healthcare organizations.
- It’s estimated that 1 in 5 internet users are exposed to approximately 1 billion emails each year, and this number is only expected to rise in the coming years as new threats emerge.
- In just the first six months of 2022, there were over 236.1 million attacks involving ransomware across the globe.
- In 2021, one in two American accounts was corrupted.
- In 2022, data breaches costed the firms around $4.35 million.
- Around 39% of UK companies said they had experienced a cyberattack in the year 2022.
- One in ten US businesses had no protection against cyberattacks resulting in zero cybersecurity assurance.
- In 2022, cybercrime made UK firms experience an average loss of £4200.
- Malware attacks peaked at 358% in 2020 compared to 2019.
- Studies found Phishing to be the most prevalent cyber hazard affecting organizations and people.
As you can see, the statics of cyber security is not that old; rather, not even a year has been spent. Many affected organizations must still cope with the losses due to cyber-attacks.
Organizations must prioritize cyber security measures to keep data secure, including frequent patching of systems, implementing advanced authentication measures, and strengthening their defenses against malware.
Recommended: Secure SDLC Approach For Preventing Cyber-Attacks
Additionally, users should ensure that their devices have the latest security updates and use a trustworthy anti-malware program to protect against cyber threats.
Overall, the statistics for cyber security in the upcoming years are bleak, but companies and individuals can do their part to secure their data. By staying alert and current on the latest security trends, businesses can protect their customers and their own sensitive information from the ever-evolving cyber threat.
Stats of Windows and Chrome for Cyber Security in 2023
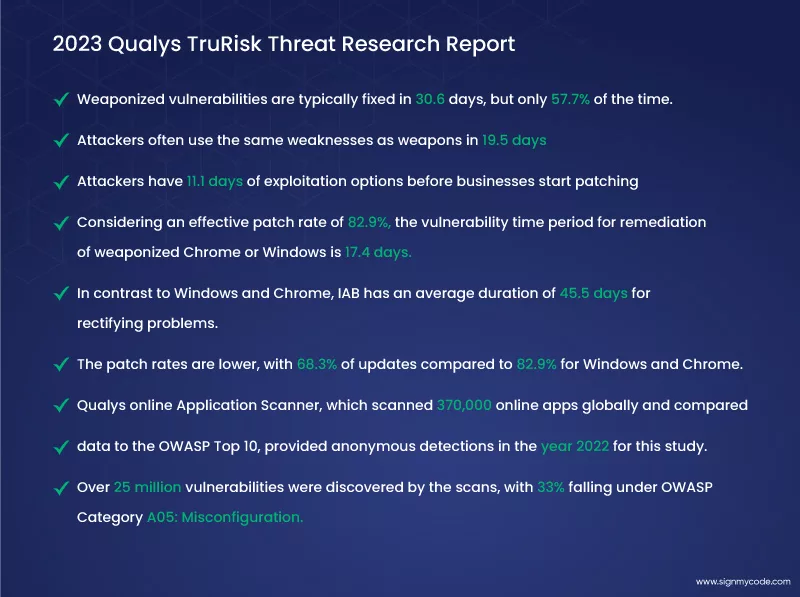
For the 2023 Qualys TruRisk Threat Research Report, the Qualys Threat Research Unit (TRU) collected and compiled information from more than 2.3 billion anonymized vulnerabilities discovered globally in 2022.
- According to the Qualys TruRisk Research Report, weaponized vulnerabilities are typically fixed in 30.6 days, but only 57.7% of the time.
- Attackers often use the same weaknesses as weapons in 19.5 days. This indicates that attackers have 11.1 days of exploitation options before businesses start patching.
- Considering an effective patch rate of 82.9%, the vulnerability time period for remediation of weaponized Chrome or Windows is 17.4 days. Patch updates for Windows and Chrome happen twice as quickly and frequently as for other programs.
- In contrast to Windows and Chrome, IAB has an average duration of 45.5 days for rectifying problems. Additionally, the patch rates are lower, with 68.3% of updates compared to 82.9% for Windows and Chrome.
- The Qualys online Application Scanner, which scanned 370,000 online apps globally and compared data to the OWASP Top 10, provided anonymous detections in the year 2022 for this study.
- Over 25 million vulnerabilities were discovered by the scans, with 33% falling under OWASP Category A05: Misconfiguration.
- Among the leading causes of data breaches and a significant portion of web application flaws are misconfigurations or faults that are accidental acts by an inside party.
Issues with Cybersecurity that Organizations Frequently Face
It’s hardly surprising that there have been a record amount of data breaches in 2020; as a result, an estimated 36 billion records have been made publicly available. Organizations must remain current on the newest security threats to secure their networks and data since cybersecurity is more crucial than ever.

However, companies need to know the typical problems they’ll probably encounter while trying to defend their systems from malicious attacks.
The employment of malware and dangerous software by online attackers is one of the most frequent problems they cause. Such an attack aims to get access to confidential data, commandeer accounts, and modify data.
Distributed denial-of-service (DDoS) attacks, which may be used to overburden network resources and interrupt services, are another threat that businesses must be aware of.
Phishing is another common attack involving using fraudulent emails to get confidential data. Phishing emails might seem real, making it challenging to spot them.
These emails frequently contain harmful links that, if opened, can install malware on a company’s computers and cause data loss and other possible harm.
Businesses must be mindful of the dangers posed by employee neglect. Weak passwords and exposing private information across insecure channels are examples of poor computer security practices that can make a network vulnerable to attack.
Recommended: Top API Security Best Practices to Prevent Security Threats
Additionally, uncontrolled access to sensitive data might jeopardize a business’s data.
Organizations and companies that want to protect their networks against cyberattacks must deal with many intricate problems.
Fortunately, various viable solutions exist to address these issues, including using multi-factor authentication, stronger passwords, enhanced staff knowledge and training, and routine security checks.
A Threat to Organization’s Cyber Space

Cyber crimes are a genuine danger to organizations of all kinds. These attacks have a growing economic impact.
According to Hiscox’s research from 2019, a cyberattack typically costs roughly $200,000.
A recent U.S. Small Business Association poll revealed that 88% of small business owners believe their operations are vulnerable to a cyber assault. This becomes especially alarming for owners of small businesses.
Various security issues exist in the modern business environment. The following need to be better understood by organizations:
- Social engineering
- Cloud computing
- Ransomware
- Distributed denial-of-service (DDoS)
- Artificial intelligence (AI)
- Machine learning (ML)
- Third-party software
- Cryptocurrency and blockchain
Each of these needs a proactive strategy to guard against dangers like malware, illegal access, and data leakage. It’s also critical to remember that security precautions need to be updated often to be effective.
How can Businesses be Proactive in Preventing Cyberattacks?
Nowadays, businesses must be proactive in thwarting cyberattacks. Companies of all sizes may better defend their cyberspace and lessen the financial effect of cyberattacks.
It can be done by utilizing the latest security technologies, keeping staff members informed and trained, and hiring a reputable security company.
Now, let us look at each measure carefully.
Social Engineering for Hacking Activities
Organizations must be aware of the possible hazards posed by social engineering and take the appropriate precautions to shield themselves against cyberattacks.
The term “social engineering” describes the use of psychological trickery and other strategies to trick consumers into disclosing sensitive information. Additionally, they can manifest in a number of nefarious actions, such as phishing attempts, which account for 91% of social engineering attacks.

To successfully reduce the hazards social engineering poses, organizations should utilize preventative measures, including the following:
- User training
- Policy formulation
- Security software
User training is crucial to any organization’s security against social engineering charges. Employers should educate staff members on how to spot phishing and other social engineering techniques. Examples and recommended methods for identifying dubious activity and avoiding harmful links should be covered in this course.
The rules and procedures of the company involving private information, passwords, and data encryption, should be made plain to employees by the employer.
Organizations should create thorough security rules to safeguard their data and systems in addition to user training. These rules have to provide instructions for recognizing and avoiding social engineering attacks and steps for handling security issues.
Organizations must ensure their security policies are routinely reviewed and updated to reflect the most recent best practices.
Lastly, businesses should spend money on security software programs to identify and prevent social engineering attempts. Security software can spot suspicious emails and other behaviors and warn businesses about potential risks.
Anti-phishing and anti-malware technologies, for example, may shield businesses from harmful activity while protecting user privacy.
The Internet of Things (IoT) and Issues of Cloud Computing
Businesses and organizations confront escalating cybersecurity risks, particularly in the context of cloud computing. In recent years, the amount of important data kept across various data sources has increased tremendously. As the number of devices used to hold sensitive data rises, so does the risk of data breaches and other security risks.
Recommended: Ensure IoT Identity Security at Scale with the Excellence of PKI
Particularly with regard to cybersecurity, cloud computing has created a number of new challenges that must be resolved to safeguard the organizations that rely on it.
The fundamental issue with cloud computing is that its resources and data are available almost everywhere, even in potentially unsafe areas. As a result, several hazards might arise, such as hostile assaults, unauthorized access, and data loss.
Recommended: What is Azure IoT Security? Top Best Practices to Secure IoT Devices
Organizations must have a thorough security plan in place to counter these attacks. This strategy should incorporate security precautions, including data encryption, access control setup, and network activity monitoring.

Additionally, the Internet of Things (IoT) has brought up a unique set of cybersecurity problems. Businesses must consider the possibility of data breaches and harmful attacks as more “smart” gadgets are connected to the internet.
Ensuring that these smart devices are adequately protected and under constant observation is crucial to avoid illegal access and data loss.
No of the size of the firm, security must always come first. Organizations must establish thorough security measures to counter these dangers as the possibility of data breaches and other attacks rises.
The IoT and cloud computing have revolutionized corporate processes and the quantity of data. This information can be stored and accessed, but they have also raised new cybersecurity issues that must be handled.
Ransomware Attacks
Hackers that use ransomware seize control of data or computer systems. Until the affected individual or organization pays a ransom, they might hold your device or information hostage.
Hackers use a number of methods to get into a system, including sending malicious emails, clicking on malicious online ads, taking advantage of network flaws, or visiting a website that has been compromised.

Organizations must be aware of the risks of ransomware and take precautions to lessen the likelihood of a successful attack.
Businesses should inform their personnel about the dangers of ransomware and encourage safe internet habits, including avoiding dubious links and emails.
Organizations should also spend money on the newest security tools to guard against ransomware and other online dangers. Systems that detect intrusions, virus protection, data backups, and firewalls should all be part of these technologies. To ensure network security, software and system upgrades must be applied on a regular basis.
Recommended: Cyber Security Vs Software Security Vs Application Security
By taking precautions, businesses may greatly reduce their risk of a ransomware attack. Additionally, firms must have a strategy in place for both responding to an attack and averting another in the future.
Although investing in cyber security is not simple, the effort is well worth it to protect business data.
Distributed denial-of-service (DDoS) attacks
Distributed denial-of-service (DDoS) teaming up with hostile actors to overload a network or system is becoming increasingly dangerous to organizations. With the advancement of technology, this malevolent technique of assault has gotten more complex and can expose businesses to vulnerabilities.
To defend against these kinds of attacks, enterprises must stay current on cybersecurity developments. DDoS attacks subject networks, devices, and systems to waves of simultaneous requests, leaving them very open to attack.

Organizations must invest in systems to identify malicious activity and warn them of an attack if they are to safeguard against these kinds of dangers. Organizations should also ensure that the network is appropriately set up and that the most recent security patches and upgrades are installed.
Finally, businesses should ensure that security precautions are taken to lessen the impact of successful assaults. Businesses will be well-equipped to defend against DDoS assaults by integrating these cybersecurity measures.
Artificial Intelligence and Machine Learning in Organizations
Cybercriminals employ machine learning (MI) and artificial intelligence (AI) to create increasingly refined yet still successful cybercrimes.
These tools are a priceless resource for individuals who wish to damage others since they may be used to “learn” the most efficient assault strategies. Fortunately, artificial intelligence and machine learning may also be effective tools in the fight against cyberattacks.
These technologies enable cybersecurity experts to foresee, identify, and thwart possible attacks before they have a fatal effect.
AI-driven security systems are improving at seeing abnormalities, identifying malicious conduct, and taking immediate action in the face of threats. AI and machine learning can also automatically evaluate massive volumes of data to find possible security flaws.
Utilizing these cutting-edge cybersecurity technologies can help safeguard enterprises from attacks and lessen their effects.
Third-party Software for Cyber Security
Small businesses are an appealing target for cyber attackers due to their smaller computer infrastructures which can provide gateways to bigger targets, and the lack of robust security protocols in place.

An example of this is the Target breach of 2013 which originated from a cyber attack on a small business that serviced Target’s heating and air conditioning, resulting in 40 million stolen credit and debit card numbers. It also included the theft of about 70 Million personal records comprising personal information.

Organizations that utilize third-party software to ensure cybersecurity can be one of the most effective ways to prevent such cybercrime. Many software providers have incorporated advanced security features such as multi-factor authentication, encryption, and threat detection to protect small businesses from cyber attackers.
Additionally, these third-party cybersecurity services can help detect, respond, and remediate incidents quickly, ensuring that businesses and their customers are safe.
Mostly, small businesses are an attractive target for malicious actors due to their lack of robust security protocols. However, by utilizing the right third-party cybersecurity software, they can ensure they are properly protected, and their customers can keep their data safe.
Cryptocurrency and Blockchain Technology
Blockchain technology and cryptocurrencies are rapidly being used in businesses. Businesses are drawn to cryptocurrency and blockchain technology because they provide a safe and dependable way to store data and conduct transactions.
However, as this technology develops, the risk of hacks also grows. Having the appropriate cybersecurity measures in place is crucial to safeguarding the investments made by your company.
There are several ways that blockchain technology and cryptocurrencies might be applied within enterprises to improve cybersecurity. First, good encryption can prevent bad actors from viewing or stealing sensitive data, such as account passwords.

Additionally, businesses may securely manage and preserve investment-related data using blockchain technology. This guarantees that all data associated with a specific transaction is safe and that only people with the proper authorization may access it.
Blockchain technology also assists businesses with user authentication management. Organizations possibly lower the risk of data breaches by keeping track of user authentication data in a secure, decentralized database and guaranteeing that only confirmed users have access to critical information.
Additionally, blockchain technology may provide businesses with real-time data on their investments and transactions. This will provide a degree of transparency that boosts consumer confidence.
Overall, using blockchain and cryptocurrency in enterprises is becoming increasingly crucial for attaining strong cybersecurity. Data storage and protection using blockchain technology and cryptocurrency are safe and dependable.
Additionally, it can deliver genuine information and enhance the verification of users. Organizations must prioritize their cybersecurity efforts to secure their data and assets in light of the rise of cyberattacks and the elevating value of cryptocurrencies.
Wrapping up
Ultimately, you can protect your organization in 2023 by investing in cyber security and with cyber security best practices such as use Code Signing Certificates to protect your software or app and follow security best practices while development!

