What are the Diverse Types of Code Signing Certificates?
Last Modified: September 18, 2024
Code Signing Certificates are an essential part of the software security process. It is a form of digital signature that verifies to customers and other users of the software that the code has not been tampered with and remains secure.
Code signing certificates come in three different types: Organization Validation (OV), Standard, and Extended Validation (EV). To understand them, we need to get to the basics of code signing and how it can change your life. So, let us get started.
What is Code Signing Process?
The process of code signing involves digitally signing a software binary or file with a digital signature to ensure its authorship or publication. It helps to ensure the integrity of the file and prevent unauthorized changes or tampering after it has been signed.
This is especially important in the case of applications that are designed for internal or external use, as well as updates, repairs, and testing.
Process of Code Signing
First, the time and date of code signing are recorded with a cryptographic hash algorithm. This algorithm allows the code author to generate a unique “fingerprint” that is uniquely associated with the software binary.
Second, the code author digitally signs their code with their personal signature, providing a non-forgeable assurance of its authorship. Finally, the code is published, providing users with a secure way to install the software file.
Overall, code signing is an essential part of thwarting malicious attempts to infiltrate systems or data. By adding a digital signature to the software, users can trust that the code can be trusted and is safe to install.
How Code Signing is a Crucial Process in Cybersecurity?
Code signing is an important security measure for software publishers and users. It uses a public/private key pair, a Certificate Authority (CA), and a digital certificate to help protect users from malicious code.
Recommended: Impact of Code Signing on Your Organization
When a code signing certificate is issued to a software publisher, it contains the publisher’s name, public key, and the CA’s signature attesting to the identity verification by the CA.
The software’s hash is then signed using the publisher’s private key to create a digital signature. This signature helps users verify that the software is from a trusted source.
When a user downloads the software, the code signing certificate and digital signature are then checked to make sure the software hasn’t been modified or tampered with. This helps users know that the code hasn’t been modified or corrupted and is safe to install.
Code signing provides users with an extra layer of security when downloading software, ensuring that the software is from a trusted source and hasn’t been modified. It also helps publishers protect their software from malicious tampering.
How does Code Signing Work Out?
Just as other PKI methods, code signing uses the following:
- Public or Private key pair
- A Certificate Authority
- A Digital Certificate
Software signed by a publisher is contained in a confined package together with a code signing certificate as well as a digital signature. A code signing certificate usually includes the publisher’s name, public key, and even the CA’s signature attesting to the identity verification by the CA.
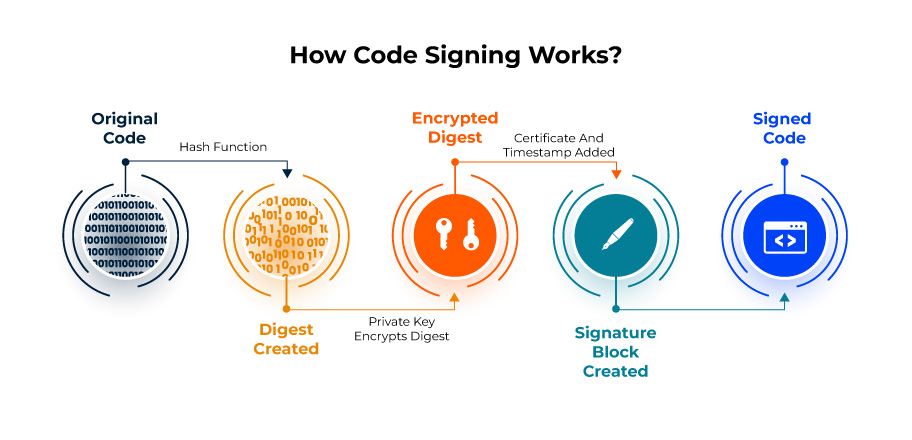
The software’s hash has been signed with the publisher’s private key to create a digital signature. The user agent will examine the certificate regarding validity and integrity once the program is delivered (analyzing if the software has been modified since it was signed). The hash inside this digital signature is revealed using the public key in the Code Signing certificates.
Next, it checks the software’s most recent hash calculation to compare it with the digital signature hash. The buyer or customer is certain that the program has not been changed by verifying that the hashes match.
Code signing requires a crucial security component known as private key management. Cybercriminals may exploit the key to sign harmful code and distribute it as updates to the developer or customer systems if it is stolen or improperly stored.
What are the Three Types of Code Signing Certificates?
Now that you know the meaning, working, and importance of Code Signing Certificates, you must be wondering about their types and how they differ from each other. So, continue reading below to seek answers to every question.
EV Code Signing Certificate
An EV Code Signing Certificate is an advanced digital certificate offering organizations enhanced security features. It is a favorite among IT professional organizations when they need to obtain the highest level of source code protection.
This type of certificate includes a Hardware Token that stores the private key details and significantly increases security. It is easy to use and set up with individual and organizational certificates.
What sets the EV Code Signing Certificate apart is that it allows users to restrict access and put the private key behind a token. This extra layer of security makes the certificate even more reliable, as the key can only be retrieved with the authentication of the physical device.
It is an excellent way for businesses to safeguard their code and applications from unauthorized access.
| Product Name | Price |
| Comodo EV Code Signing Certificate | $279.99/yr |
| Certera EV Code Signing Certificate | $279.99/yr |
| Sectigo EV Code Signing Certificate | $279.99/yr |
| DigiCert EV Code Signing Certificate | $559.99/yr |
Individual (IV) Code Signing Certificate
Do you want to publish a program but don’t belong to any organization? If so, Individual Validation Code Signing Certificate is the perfect choice for you. This type of certificate offers the same level of security as an ordinary code signing certificate but is crafted specifically for an individual publisher.
The IV code signing certificate ensures that system warnings are disregarded, giving end-users a smooth and seamless experience. It also helps to protect your file or application against any malicious activity and prevents tampering.
This type of certificate is recommended for anyone looking to protect their programs and applications from unauthorized use.
With an IV code signing certificate, you can rest assured that your program is secure and your end users are safe from malicious activities. So, this is the perfect solution if you’re an independent publisher.
| Product Name | Price |
| Comodo Individual Code Signing Certificate | $219.99/yr |
| Sectigo Individual Code Signing Certificate | $219.99/yr |
Standard Code Signing Certificate
The Standard Code Signing Certificate is one of the companies’ most important digital certificates. It is also known as an Organization Validation Code Signing Certificate. When a company launches a product, this type of certificate is preferred.
Enterprises need to be CA-authenticated, as it helps them build trust and reputation with the operating systems that recognize their software.
The company must provide the CA with a Certificate Authority, phone number, financial information, and residential address with its government registration to obtain the Standard Code Signing Certificate.
The Standard Code Signing Certificate also ensures that the software is free from any malicious changes or tampering since it has been digitally signed. This is one of the most important features of the certificate, as it helps protect users from potential security threats.
Therefore, for companies launching their products, a Standard Code Signing Certificate is an important and cost-effective tool to ensure their applications are trusted, secure, and reliable.
| Product Name | Price |
| Comodo Code Signing Certificate | $219.99/yr |
| Sectigo Code Signing Certificate | $219.99/yr |
| Certera Code Signing Certificate | $215.99/yr |
| DigiCert Code Signing Certificate | $399.99/yr |
How does Code Signing Certificates Benefits Secure Software, Apps, and Websites?
Code signing certificates are essential for any software, application, or program developer, as it not only help protect the program from malicious attacks but also provide various key features and benefits such as improved brand recognition, confirming the origin and consistency of code or software, almost no security warnings, decreased maintenance costs and compatibility with 64-bit and 32-bit software and apps.
- Improved brand recognition is essential for companies that want to build trust and credibility with their customers.
- By verifying the origin and integrity of the software, customers can be sure that the source is trustworthy and that the product is genuine.
- Additionally, code signing certificates confirm the consistency of the code and ensure users that the code has not been altered or tampered with. This greatly reduces the risk of malicious software, which can damage a user’s system considerably.
Wrapping up
We hope you have now analyzed the significance of Code Signing Certificates.
Recommended: Standard Vs EV Code Signing Certificate
Buy Code Signing Certificate
Increase your Software Downloads and Verify its Integrity by Digitally Sign Software and Executables using Trusted Code Signing Certs.
Price Starts at $215.99 Per Year

