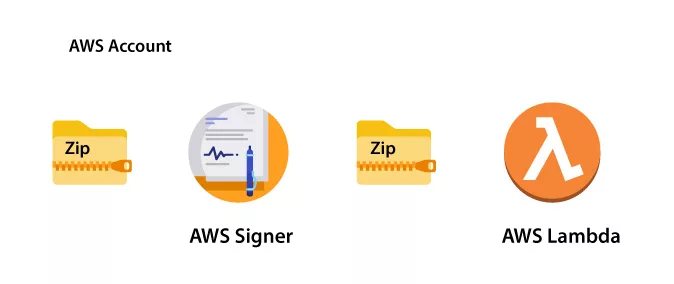
What is Lambda Code Signing?

By enabling code signing, you can guarantee that only trusted code is executed within your functions. Lambda meticulously examines each code package during deployment and verifies that a reliable source has signed it.
Please note that code signing is not supported for functions defined as container images. This means that code signing cannot be utilized if you use container images for your Lambda functions.
To maintain code integrity, AWS Signer is the recommended tool for creating digitally signed code packages for both functions and layers.
Recommended: How to Use Microsoft SignTool with AWS CloudHSM to Digitally Sign Authenticode Files?
Whenever a user attempts to deploy a code package, Lambda conducts comprehensive validation checks on the code package before accepting the deployment.
It is important to note that these code signing validation checks are performed during deployment, ensuring no impact on the performance of function execution.
A Quick Glimpse of AWS Lambda
AWS Lambda is an Amazon Web Services (AWS) serverless computing service. It enables you to run your code without provisioning or managing servers. With AWS Lambda, you can concentrate completely on creating application code while AWS manages infrastructure, scalability, and availability.
Lambda functions are event-driven and have a brief lifespan. You may submit your code to Lambda in the form of functions, and the service will run them in response to particular events or triggers.
AWS services such as API Gateway, S3, DynamoDB, or bespoke events from your own applications can be triggered.
Some of AWS Lambda’s Primary Features and Benefits
- Get a Serverless Architecture with Lambda! You don’t have to worry about server administration, patching, or scalability. AWS handles the infrastructure, enabling you to concentrate on creating code.
- Lambda functions are triggered by events like changes to data in an S3 bucket or an HTTP request using API Gateway. With this event-driven design, you can create extremely scalable and responsive apps.
- AWS Lambda has a pay-per-use pricing model, which means you only pay for the actual computing time your functions utilize. There are no setup fees or minimum payments, making it affordable for applications with changing workloads.
- Scaling automatically: Lambda scales your functions in response to incoming requests. It allocates the computing resources required to handle the demand, and you don’t have to manage the scaling process manually.
- AWS Lambda supports a variety of programming languages, like Python, Node.js, Java, C#, Ruby, PowerShell, and Go. You can select the language that is most suited to your application and development needs.
- Lambda works easily with other AWS services, allowing you to develop serverless architectures and event-driven processes. Lambda may be used with services such as S3, DynamoDB, SQS, SNS, and others to construct powerful and scalable applications.
- AWS Lambda has monitoring and logging features. AWS CloudWatch allows you to gather metrics, create alerts, and analyze logs, giving you visibility into the performance and behavior of your operations.
Why do you Need AWS Signer?
AWS Signer is utilized for creating signing profiles. These are used to generate the signed code packages. AWS Identity and Access Management (IAM) provides tools and controls to control the process of signing code packages and creating signing profiles.
Refer to the “Authentication and Access Control section” in the AWS Signer Developer Guide.
Enabling code signing for a specific function involves two main steps. First, you must create a code signing configuration that outlines a list of allowed signing profiles.
Recommended: How to Configure your Code Signing for AWS Lambda?
Then attach it to the desired function. The code signing configuration defines the appropriate policy action if validation checks fail.
Lambda layers adhere to the same format as signed code packages for function code. When you include a layer in a function with code signing enabled, Lambda verifies that an approved signing profile signs the layer.
It is important to note that when you enable code signing for a function, all layers added to that function must be signed by one of the authorized signing profiles.

What is the Role of IAM?
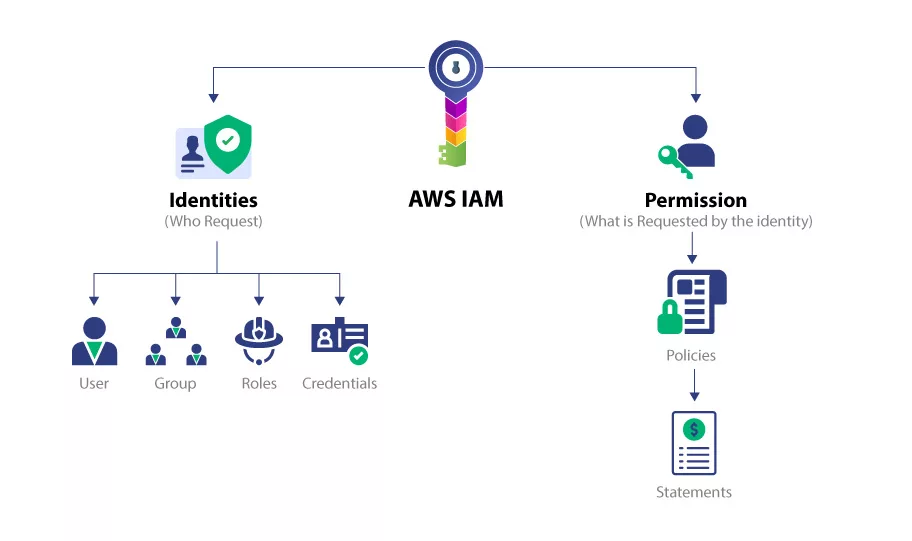
IAM provides the necessary tools to control the creation of code signing configurations. It is recommended to assign this ability only to specific administrative users. Additionally, you can enforce policies within IAM to ensure that developers can only create functions with code signing enabled.
If you wish to keep track of code signing changes, you can configure it to log events to AWS CloudTrail. Successful and blocked deployments to functions are recorded in CloudTrail, providing valuable information about the signature and validation checks performed.
Configuring code signing for your functions can be done through various methods such as the Lambda console, AWS Command Line Interface (CLI), AWS CloudFormation, and the AWS Serverless Application Model (SAM). Choose the method that suits your workflow and preferences.
It is essential to highlight that no additional charges are associated with using AWS Signer or enabling code signing for AWS Lambda. You can leverage these features without extra costs, making it an economical choice for securing your Lambda functions.
What is the Validation Checks of Lambda?
During the deployment process of a signed code package to your Lambda function, Lambda performs several validation checks to ensure the integrity and validity of the code. These validation checks are as follows:
Integrity:
Lambda validates that the code package has not been altered since it was signed. It is done by comparing the hash of the package with the hash obtained from the signature.
Expiry:
Lambda checks whether the signature of the code package has expired. This validation ensures that only valid and up-to-date code packages are deployed.
Mismatch:
Lambda verifies that the code package is signed with one of the allowed signing profiles specified for the Lambda function. A mismatch occurs if the signature is absent or doesn’t match any of the allowed signing profiles.
Revocation:
Lambda validates that the signature of the code package has not been revoked. This ensures the code package is still trustworthy and has not been compromised.
Two Actions that the Policy Offers
The actions taken by Lambda when any of these validation checks fail determined by the signature validation policy defined in the code signing configuration. The policy offers two possible actions:
Warn:
If a validation check fails, Lambda allows the deployment of the code package but issues a warning. This warning is logged in Amazon CloudWatch as a new metric and stored in the CloudTrail log. It serves as a notification about the potential issue with the code package.
Enforce:
Lambda issues a warning when a validation check fails. Lambda blocks the deployment of the code package. This ensures only valid and trusted code is executed within the Lambda function.
It’s worth noting that while you can configure the policy for expiry, mismatch, and revocation validation checks, the integrity check cannot be configured. If the integrity check fails, Lambda automatically blocks the deployment, as tampered code poses a significant security risk.

